Zscaler ZPA at the ingress versus Illumio-style micro‑segmentation inside the organisation: what’s different, what each stops, and how to use both
Most modern compromises don’t succeed because attackers “can’t get in”; they succeed because, once they have a foothold, they expand impact by moving laterally across internal paths. Zero Trust thinking targets that problem by rejecting implicit trust based on network location and shifting protection to the resource and the session.
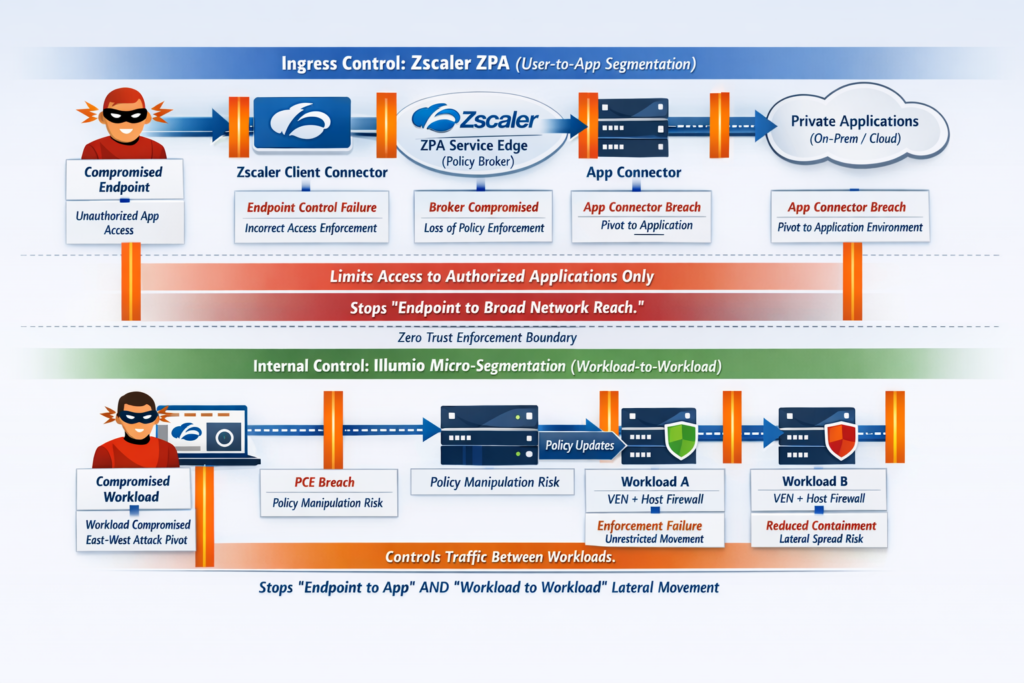
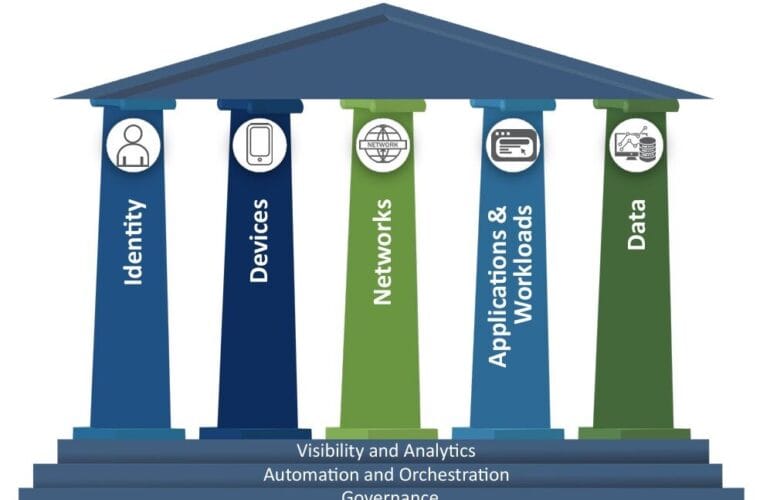
Two control families are often described as “lateral movement reducers”, but they operate at different points in the attack path:
- ZTNA user‑to‑app access brokers at the edge/ingress (such as Zscaler Private Access, ZPA) focus on granting access to specific private applications without placing a user device “on the network”.
- Micro‑segmentation / Zero Trust Segmentation inside the environment (such as Illumio Core) focuses on understanding and controlling workload‑to‑workload communications (east‑west) using a central policy plane and local enforcement on workloads.
This difference is fundamental. ZPA primarily constrains what a user device can reach at the moment it requests access to private apps. Illumio-style micro‑segmentation primarily constrains what systems can talk to what other systems once internal reach exists, limiting east‑west spread after initial compromise.
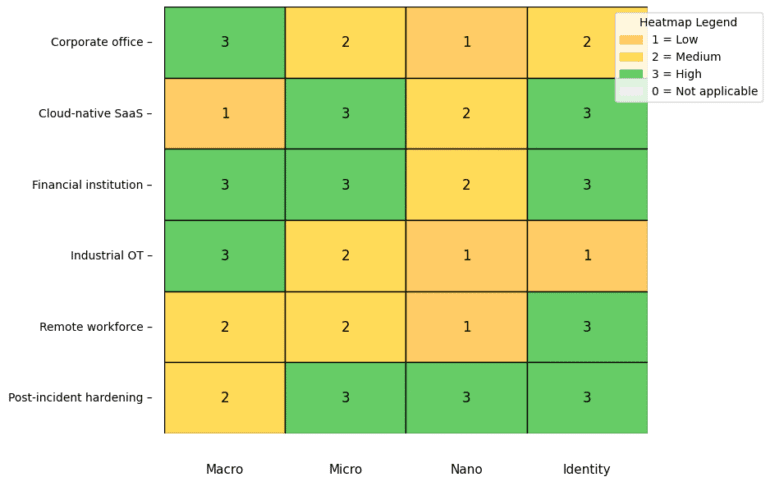
The shared objective: reduce blast radius by removing implicit trust
Zero Trust Architecture guidance is explicit that network location (inside vs outside) should not grant trust. Authentication and authorisation occur before establishing access to a resource, and defences are organised around protecting resources rather than assuming a trusted internal network.
Segmentation is one of the most direct ways to convert that principle into engineering reality. Broad segmentation guidance describes segmentation as “damage limitation in space”: if one device is compromised, boundaries prevent it from reaching everything else.
ZPA and Illumio both contribute to this goal, but they enforce controls in different places and at different layers.
Zscaler ZPA: limiting lateral movement near endpoint ingress points
What ZPA is optimised to do
Zscaler Private Access is positioned as a cloud-delivered ZTNA service for secure access to private applications hosted on‑prem or in public cloud. Its principles include application access based on context without requiring network access, inside‑out connections that make applications “invisible” to unauthorised users, and application segmentation intended to limit lateral movement.
The practical outcome is a replacement for VPN-style network extension. Instead of giving a device a routable position inside the corporate network (and therefore broad adjacency), ZPA aims to connect authorised users to specific applications through policy-controlled sessions.
How ZPA works at a high level (and why it matters for lateral movement)
ZPA’s architecture is commonly described as a broker model: a user component and an application-side component each establish outbound connections which are stitched together by a service edge after policy checks (including identity and device posture). This “inside‑out” pattern reduces the need for inbound exposure of applications.
From a lateral movement standpoint, the critical shift is that the user/device is not placed “on the network” in the VPN sense. If the endpoint is compromised, attackers typically try to enumerate, scan, and pivot to adjacent internal targets. ZPA’s user‑to‑app model is designed to reduce those opportunities because access is scoped to what policy permits and applications are intended to be reachable only via the brokered path.
Policy and segmentation concepts in ZPA
ZPA’s administration model uses application segments and segment groups to define what constitutes an “application” (for example, by FQDNs, IPs and ports) and then apply policies so specific users or groups can access those applications. Configuration guidance centres on defining application segments, associating them with server groups and connector groups, then applying policies to control access.
ZPA is also positioned as enabling segmentation “without needing to segment the underlying network”, emphasising least-privileged access to discrete applications and reduced lateral movement opportunities compared with broad network access models.
The “lateral movement” ZPA is best at preventing
When organisations say “ZPA prevents lateral movement”, they usually mean lateral movement that originates from the user edge as a result of VPN-style network presence. ZPA contrasts VPN (which assigns an IP address and places the user on the network) with ZPA (which connects the user only to allowed applications, without access to adjacent systems).
In practice, ZPA is strongest at reducing:
- Endpoint‑initiated scanning and pivot attempts that depend on broad network adjacency, because the endpoint is not granted general network-level access.
- Discovery by addressability, because applications are intended to be not visible or reachable to unauthorised users.
- Over-privileged remote access patterns, by scoping policy to user-to-app access rather than to a whole subnet or VLAN.
This does not automatically mean all lateral movement inside the environment is addressed. That depends on what happens after an attacker compromises internal systems and starts moving east‑west.
Illumio-style micro‑segmentation: limiting lateral movement inside the organisation
What Illumio-style micro‑segmentation is optimised to do
Illumio positions its approach as Zero Trust Segmentation across cloud, data centre, and endpoint devices, emphasising unified visibility and control and highlighting that the agent is not inline to traffic.
Micro‑segmentation addresses a different problem from ZTNA-at-ingress: it aims to control east‑west traffic paths between systems inside the estate. If one server is compromised, micro‑segmentation is designed to stop that server reaching unrelated peers, management services, databases, or file shares unless explicitly allowed.
Illumio Core architecture in brief: PCE and VEN
Illumio Core is described as consisting of two key components:
- Policy Compute Engine (PCE), the central policy controller and manager of enforcement.
- Virtual Enforcement Node (VEN), an agent installed on workloads that collects flow and metadata and receives policy from the PCE to program the workload’s native host firewall.
The architecture also emphasises that the VEN is not inline to traffic and does not route traffic, and that segmentation rules are enforced using the native stateful L3/L4 firewalls on workloads.
Visibility-first and staged enforcement
A major practical challenge in micro‑segmentation is understanding dependencies: what really needs to talk to what. Illumio documentation describes workload policy states (including states used for installing/activating and for visibility without blocking), supporting a phased approach where you gain traffic visibility and build policy before enforcing deny/allow rules.
This phased approach aligns with how micro‑segmentation programmes typically succeed: map communications, reduce unknown and unnecessary flows, then enforce least privilege to prevent lateral movement.
The “lateral movement” micro‑segmentation is best at preventing
Micro‑segmentation is purpose-built to constrain east‑west movement. General segmentation guidance highlights that once attackers compromise an endpoint or server, they quickly scan and attempt to reach high-value assets. Without segmentation, a flat internal network can allow wide reach; with segmentation, attackers are forced to breach multiple boundaries.
Illumio’s model supports this by enforcing policy on the workloads themselves via their host firewalls, meaning controls can apply even when traffic does not traverse a central chokepoint.
The crux difference: user‑to‑app segmentation versus workload‑to‑workload segmentation
ZPA is explicit about “user-to-app segmentation” and contrasts it with VPN models that place users on the network.
Illumio is explicit about building segmentation based on workloads and enforcing through host firewalls via its policy compute and enforcement architecture.
This difference means the two approaches answer different operational questions:
- ZPA asks whether a user on a device should be allowed to access a specific private application right now, and provides a brokered session to do so without exposing the broader network.
- Illumio asks whether one workload should be able to communicate with another workload on specific ports/protocols, and enforces that decision at the workload’s firewall to restrict east‑west spread.
Both reduce lateral movement, but in different parts of the environment and against different pivot patterns.
Enforcement point comparison: brokered access path versus host firewall control
ZPA enforcement characteristics
ZPA’s model is based on brokered sessions between user and application, using outbound connectivity from connectors and policy evaluation based on identity and posture. The design emphasises inside‑out connectivity and the goal of making private applications unreachable to unauthorised users.
The enforcement effect is strongest for user‑initiated access to private apps: it is an access decision and a session construction mechanism, not a general-purpose east‑west firewall for every internal path.
Illumio enforcement characteristics
Illumio’s model enforces policy locally using the workload’s native host firewall, with a central manager and policy compute plane distributing rules to agents. The approach emphasises that enforcement is not inline to traffic.
The enforcement effect is strongest for workload‑to‑workload communications: it governs east‑west connectivity across data centre and cloud, provided workloads are represented and enforcement is in place.
Failure modes and what each approach doesn’t cover alone
Where ZPA is not a full substitute for micro‑segmentation
ZPA is designed to stop the classic VPN problem where endpoints are placed on internal networks and can laterally traverse. That’s a major win for ingress-driven risk.
However, if an attacker compromises an internal server (through vulnerability exploitation, misconfiguration, credential theft, or supply chain compromise), their next steps are typically east‑west: moving from server to server, searching for identity infrastructure, sensitive data stores, and administrative interfaces. That is the domain where segmentation guidance and micro‑segmentation solutions focus: limiting what can talk to what inside the estate to contain the breach.
Where micro‑segmentation is not a full substitute for ZTNA at ingress
Micro‑segmentation can constrain internal east‑west movement, but it does not inherently replace the ZTNA function of brokering user-to-private-app access and making applications unreachable unless policy permits. ZPA is specifically designed as a secure private application access service built for that purpose.
If an organisation retains VPN-style remote access that grants broad internal reach, it may still have a wide ingress-to-internal network exposure even if it improves east‑west controls. ZTNA addresses that exposure directly by changing how remote/private access is provided.
Attack-path mapping: how each approach changes outcomes
Compromised user endpoint as the initial foothold
A compromised endpoint commonly attempts to enumerate internal targets, probe services, and pivot. ZPA’s model reduces the endpoint’s ability to do that by not granting it general network-level access, instead permitting access only to authorised applications through brokered sessions.
Micro‑segmentation can also help if endpoint devices are included in the segmentation scope, but its primary value is constraining what internal resources communicate with each other and limiting east‑west spread.
Compromised internal workload (server or cloud instance)
Once a workload is compromised, attackers typically pivot east‑west to find high-value assets. Micro‑segmentation is designed for this scenario, with policy enforcement on workloads via their host firewalls to restrict communications to what is explicitly required.
ZPA generally does not sit in the path of server-to-server traffic, so it does not directly govern most lateral movement between internal workloads.
Ransomware spread and blast radius reduction
Segmentation guidance emphasises that when attackers compromise one part of a network, proper isolation prevents lateral movement into other segments and reduces blast radius.
In that context, ZPA helps by preventing remote access from becoming a broad network foothold. Micro‑segmentation helps by preventing internal spread from one compromised system to many others.
Operational reality: complexity is shifted, not eliminated
Operational considerations for ZPA
ZPA can simplify remote access architecture by removing VPN-style network extension, but it pushes work into application definition and segmentation design. Administration guidance stresses defining application segments, mapping them to servers and connectors, then applying policies so only the right users can access the right applications.
Reference architecture materials position deployment as a best-practice exercise, implying meaningful design decisions around segmentation granularity and application discovery.
Operational considerations for Illumio-style micro‑segmentation
Micro‑segmentation’s success depends on discovering dependencies and maintaining policy as applications evolve. Documentation describes workload management and policy states that support visibility and staged enforcement, reflecting a “discover, model, enforce” lifecycle.
Because enforcement is at the host firewall, your operational burden shifts to accurate workload representation, labels/identity, exception handling, and ongoing policy refinement based on observed flows.
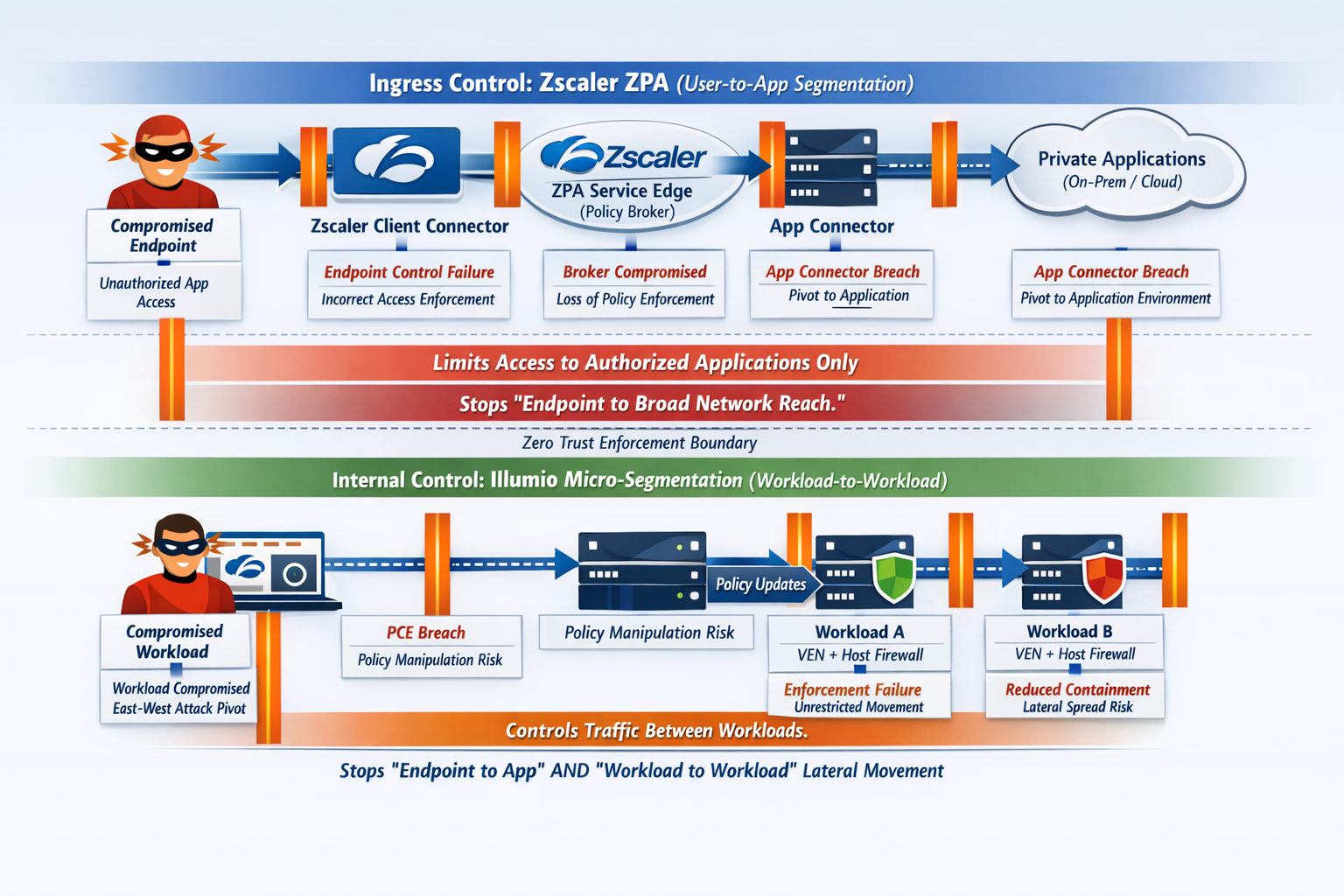
A practical decision framework: choosing the right first move
When ZPA-style ZTNA is the priority
ZTNA at ingress is usually the first priority when the dominant risk is remote access and VPN exposure. Indicators include heavy third‑party access, wide VPN network reach, and a desire to make private applications unreachable unless policy permits. Those align directly with ZPA’s principles of context-based access, inside‑out connectivity, and user-to-app segmentation.
When micro‑segmentation is the priority
Micro‑segmentation tends to be the first priority when the dominant risk is east‑west spread, ransomware blast radius, and unclear server-to-server dependencies. Those align with general segmentation rationale and with Illumio’s emphasis on mapping and enforcing workload-to-workload policy via host firewalls.
When both are true (common in large organisations)
A layered approach aligns well with the Zero Trust principle that network location should not grant implicit trust. ZTNA governs who can reach private apps at ingress; micro‑segmentation governs what can talk to what inside the estate, containing breaches even after initial compromise.
Side-by-side summary in plain language
ZPA is primarily about controlling user and device access to private applications without granting network-level presence, using policy and brokered sessions to reduce ingress-driven lateral movement.
Illumio-style micro‑segmentation is primarily about controlling workload communications inside the environment, using a central policy engine and local host firewall enforcement to reduce east‑west lateral movement and contain spread.
Key takeaways
ZPA and Illumio are both used to reduce lateral movement, but they target different lateral movement paths. ZPA is strongest where the entry point is the user device and where VPN-style network extension creates broad adjacency; micro‑segmentation is strongest where the entry point is an internal workload and where east‑west paths allow spread.
If you choose only one approach, choose based on the dominant attack path you are trying to reduce. If you are building a mature Zero Trust posture, it is common to combine ZTNA at ingress with micro‑segmentation inside the environment, because together they cover both user-to-app access control and workload-to-workload containment.
Comparison table (including combined approach + coverage map)
| Approach | Concise coverage map (lateral movement addressed where?) | Challenges / limitations | Choose this when… |
|---|---|---|---|
| Zscaler ZPA (ingress / user‑to‑app ZTNA) | Ingress / user-to-app: Strong coverage. Limits “compromised endpoint → broad internal reach” by brokering access per application rather than placing the user on a network segment. East‑west (server-to-server): Limited coverage by itself; it is not primarily an internal workload-to-workload containment control. | Requires endpoint client deployment and operational ownership. Requires deploying App Connectors near apps and maintaining the host they run on. Cutover risks include misrouted traffic, DNS misconfiguration, incomplete policies, performance regressions, and logging/visibility gaps during migration. DNS design matters: some app access modes require internal DNS via the App Connector to avoid resolution issues/loops. App Connector lifecycle constraints (e.g., avoid cloning in VM scenarios due to enrolment/key binding). | You’re replacing/reducing VPN and need secure private app access for a hybrid workforce. The biggest risk you want to reduce is remote user/contractor endpoint footholds turning into broad internal traversal. You want app-level least privilege without redesigning internal network segmentation first. |
| Illumio-style micro‑segmentation (internal / workload‑to‑workload) | Ingress / user-to-app: Not its primary scope. East‑west (workload-to-workload): Strong coverage. Controls and contains “compromised server → pivot to other servers/databases/AD/etc.” by enforcing allow/deny between workloads (typically via host firewall orchestration). | Requires deploying agents (VEN) on workloads for full enforcement; when agents can’t be installed you may need unmanaged workload representations, which can reduce how uniformly you can enforce at the endpoint/workload itself. Rollout risk: breaking legitimate dependencies if enforcement is introduced without sufficient observation/simulation. Operational challenges typical of agent-based segmentation include agent fatigue and increased operational overhead/cost. Firewall coexistence/tampering/interference is a real consideration where other tools also manipulate host firewalls; coexistence can reduce clarity/visibility in reporting. | Your dominant risk is east‑west spread (ransomware blast radius, server-to-server pivoting) in data centre/cloud. You need visibility of real dependencies and a phased “observe → simulate → enforce” path to least privilege between workloads. |
| Combined: ZPA + micro‑segmentation (recommended layered pattern) | Ingress / user-to-app: Covered by ZPA (stops “endpoint foothold → broad network reach”). East‑west: Covered by micro‑segmentation (stops “compromised workload → lateral spread”). Net effect: Reduces lateral movement both from entry points and inside the estate; constrains both “north‑south to private apps” and “east‑west between workloads.” | Complexity shifts to two policy planes and the need to keep them coherent (identity/app access policy + workload comms policy). Requires disciplined inventory, dependency mapping, staged rollouts, telemetry normalisation, change control and rollback across both initiatives. If either layer is rolled out without adequate baselining/monitoring, troubleshooting can become harder because failures can occur at ingress policy, DNS/routing, or east‑west enforcement. | You have both: significant remote access exposure and significant internal lateral-movement/ransomware concern. You want a pragmatic Zero Trust posture: ZTNA for access + segmentation for containment. You have (or can build) the operational maturity for staged rollouts and monitoring across both. |
How to implement both approaches effectively (practical, staged rollout)
Below is an implementation approach that makes the two controls complementary rather than competing, and reduces the common failure modes (access disruption, broken dependencies, policy sprawl, and visibility gaps). Where you see “should”, read it as recommended practice from real-world deployment patterns.
1) Start with a single “control objective” and scope boundaries
Define, in plain terms, what you’re trying to stop:
- Ingress objective (ZPA): prevent “endpoint compromise + remote access” from granting broad internal adjacency.
- Containment objective (micro‑segmentation): prevent “workload compromise” from spreading east‑west to other systems.
Then set scope boundaries:
- Which private apps will move behind ZPA first (non‑critical first, then critical).
- Which workload domains get segmented first (non‑critical services first, then crown jewels).
This reduces the temptation to deploy everything at once (the fastest way to create outages and alert fatigue).
2) Build a canonical inventory and dependency map (before enforcement)
This step is the single biggest differentiator between smooth and painful rollouts.
For ZPA (ingress):
- Build an inventory of applications, FQDNs, ports, authentication methods, user groups.
- Translate legacy VPN ACL intent into identity + application access rules (document exceptions and rationale).
For micro‑segmentation (east‑west):
- Build a dependency map of service-to-service flows (including periodic/batch jobs).
- Tag services/workloads with owner, environment, criticality so policy can be written in intent terms (e.g., “payments app → ledger db on 443”) rather than brittle IP lists.
Key implementation point: do not enforce micro‑segmentation until you’ve observed enough time to capture “quiet” dependencies (batch windows, backups, patching tools, monitoring, AD/DNS behaviours).
3) Deploy ZPA in a way that reduces cutover risk
A low-risk pattern is pilot → parallel run → staged cutover with explicit rollback.
Core steps that consistently prevent disruption:
- Deploy App Connectors adjacent to apps, in a redundant configuration (pairs/HA). Treat them like any other production component: patching responsibility, monitoring, capacity checks.
- Validate DNS resolution paths early. Many ZPA issues during migration are DNS-related (split DNS, internal resolution expectations, connector resolver locality, or Browser Access nuances). Resolve DNS design before broad user onboarding.
- Implement telemetry/visibility early: forward access, policy decision, and connector health logs into your monitoring stack (SIEM if available), using consistent fields (user, device, app, action, timestamp, change/change-id).
- Run a representative pilot cohort (not just friendly users) and a set of synthetic tests for critical applications (login → access → key transaction). Use pilot deny logs to refine policies.
- Keep the legacy VPN as a controlled fallback during early phases. Rehearse rollback runbooks (DNS reversal, route restore, policy revert).
Common pitfalls to avoid:
- Overly broad initial app segments (creates unintended access paths).
- Incomplete group/attribute mapping from IdP to access policy.
- “On-net” edge cases: users in offices with internal DNS and split-horizon behaviours that differ from remote.
4) Implement micro‑segmentation using “observe → simulate → enforce”
Micro‑segmentation succeeds when you treat it like a controlled engineering change, not a firewall project.
Recommended rollout mechanics:
- Start in visibility-only / audit mode to collect flows and identify dependencies.
- Draft policies using intent and identity (labels/roles/environments) so rules remain stable as infrastructure changes.
- Use simulation windows long enough to capture periodic/rare flows.
- Apply canary enforcement: pick a low-risk service group first, enforce, validate, expand.
- Automate policy management with version control and change workflow (templates/IaC where possible), so you can rollback and avoid policy drift/sprawl.
Common pitfalls to avoid:
- Enforcing too early (before dependency map stabilises).
- Treating “unknown traffic” as safe—unknown is where lateral movement often hides.
- Allowing unmanaged endpoints/legacy systems to remain blind spots without compensating controls.
5) Make the two policies coherent: align “who can reach an app” with “what the app can reach”
This is the heart of using both approaches effectively.
A practical alignment model:
- ZPA policy defines: which users/devices may access which applications.
- Micro‑segmentation policy defines: which workloads/services may talk to which other workloads/services (and on which ports).
When you combine them, you ensure that:
- A user who is allowed into an app via ZPA still cannot use that access path to laterally explore the estate, because the application tier is segmented from unrelated tiers.
- A compromised workload inside an app enclave cannot fan out, because east‑west policy constrains it—even if an attacker has credentials or finds alternate paths.
In practice, this means coordinating application onboarding with segmentation:
- When an application is onboarded into ZPA, confirm its downstream dependencies (DB, queues, identity services) are explicitly permitted east‑west—and everything else is implicitly denied.
- When segmentation is tightened, ensure ZPA test journeys still work and that any new denials correlate with recent segmentation changes (change correlation).
6) Monitoring, correlation, and rollback: treat “deny spikes” as a first-class signal
Because you are introducing controls that intentionally deny traffic, success depends on telling apart “good denies” from “bad denies”.
A strong operational pattern is:
- Establish baselines (proxy requests, auth failures, typical east‑west connection rates).
- Create alerting for:
- spikes in ZPA denies for a user/app segment,
- spikes in authentication failures,
- spikes in east‑west denies for a service,
- connector health degradation / failovers,
- synthetic transaction failures.
- Correlate denies with recent change events (policy changes, connector changes, segmentation commits). This turns “mystery outages” into “this change caused this impact”.
Rollback discipline:
- For ZPA: rollback could mean reverting a policy, restoring DNS/routing, or moving a cohort back to VPN temporarily.
- For micro‑segmentation: rollback usually means reverting a policy version or moving workloads back to a less restrictive enforcement mode while you fix the rule set.
7) A practical phased roadmap (that keeps momentum without breaking production)
A common staged path looks like:
- Phase A: ZPA pilot for non‑critical apps + micro‑seg visibility-only for a subset of workloads.
- Phase B: Expand ZPA to more apps/user groups + begin micro‑seg canary enforcement on low-risk services.
- Phase C: ZPA covers most private app access + micro‑seg enforcement expands by criticality tiers (with stronger change control).
- Phase D: Optimisation: reduce policy sprawl, tighten defaults, continuously review denies and unused accesses.