Identity is the control plane of a modern enterprise. In a merger, it becomes the fastest route to synergy—or the fastest route to disruption—because every employee, application, device, and administrator action depends on trustworthy authentication and authorisation. The key to accelerating identity integration safely is to avoid conflating Day‑1 collaboration with full consolidation. The fastest programmes deliver secure interoperability first (so both companies can work together quickly), then consolidate identities, applications, and directories in controlled waves. This approach reduces outages, limits blast radius, prevents privilege sprawl, and keeps the business productive while the technology foundation evolves.
This article explains how to accelerate integration while controlling risk, and it clearly separates integration elements that must be treated as mandatory from those that can be strategically deferred.
1) The merger identity paradox: speed comes from reducing change, not increasing it
Many identity integration efforts slow down because they start with a large, disruptive objective: “merge everything into one directory and one identity provider as quickly as possible.” That sounds decisive, but it creates a high‑risk set of dependencies: mass credential changes, simultaneous application rewiring, directory clean‑up, and permission remapping. In a merger environment—where organisational charts are changing, systems are being discovered late, and governance is still settling—this can turn into a cascade of broken access and emergency exceptions.
Counter‑intuitively, the fastest path is typically to reduce the amount of identity change required to enable collaboration. If employees can access shared resources while continuing to authenticate with their existing credentials (at least initially), you remove two common causes of delay: large‑scale credential cutovers and immediate directory consolidation. That “coexistence first” posture can be made safe when you enforce a consistent security baseline (for example, strong authentication, conditional access, and clear admin boundaries), and when you automate joiner–mover–leaver controls so access does not accumulate faster than you can govern it.
In other words:
- Acceleration comes from enabling secure access with minimal disruption to users.
- Safety comes from policy enforcement, lifecycle automation, and auditable controls across both organisations.
- Long‑term value comes from a disciplined wave plan that gradually simplifies and retires duplicate systems.
2) Define “safe acceleration” properly: not zero risk, but engineered risk containment
No complex technology programme is free of risk. A safer goal is: minimise the probability of serious incidents and minimise the impact if something goes wrong. “Safe acceleration” in identity integration means you deliberately engineer for:
- Reversibility: changes can be rolled back without dismantling the whole design.
- Isolation: early integration choices do not create unbounded lateral movement or uncontrolled privilege.
- Consistency: security policy is applied reliably, even while platforms remain separate.
- Visibility: authentication, authorisation, and admin actions are logged and monitored end‑to‑end.
- Lifecycle closure: accounts and entitlements are removed quickly when people move or leave.
These are not abstract ideals; they translate into concrete mandatory elements (covered later) and practical phasing.
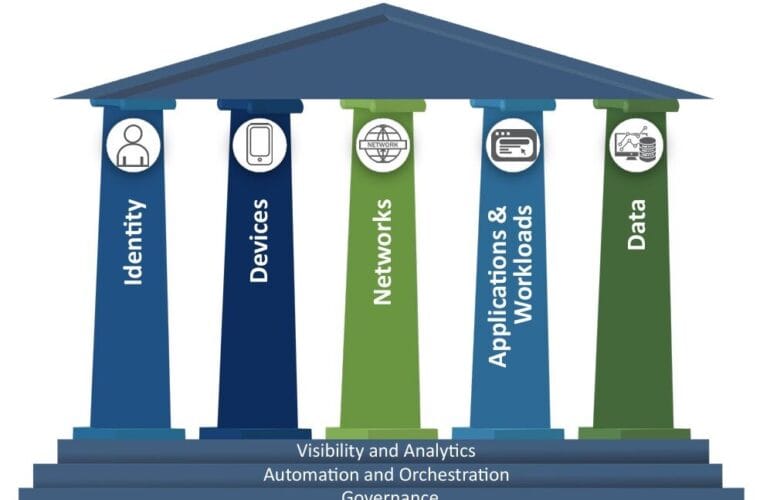
3) The three‑layer model: what to stabilise first to go faster safely
A merger identity programme is easier to execute when you separate the work into three layers and sequence them deliberately:
Layer 1: Identity control plane
This includes identity providers, directories, authentication methods, MFA, conditional access, device trust signals, session controls, and privileged administration boundaries. If this layer is inconsistent or porous, everything else becomes unstable.
Layer 2: Lifecycle and entitlements
This includes joiner–mover–leaver processes, provisioning and deprovisioning, group membership management, role assignments, and minimum viable governance. This layer stops the merger from creating permanent access sprawl.
Layer 3: Application and workload authorisation
This includes SSO standards and integrations, token configurations, provisioning connectors, API authorisation, and remediation of legacy authentication protocols. This layer is where deep consolidation work lives, and it should be approached in waves once the first two layers are stable.
Why this matters for acceleration:
You can often achieve Day‑1 productivity by getting layers 1 and 2 “good enough” with a coexistence model, while migrating layer 3 progressively. Trying to complete all three layers at once is how “fast” turns into “fragile.”
4) Safe acceleration levers that genuinely shorten timelines (without shortcuts that backfire)
Lever A: Day‑1 access via interoperability, not immediate user migration
The quickest wins come from enabling cross‑company access while leaving users in their home identity system initially. This can be done through federation, controlled cross‑tenant access, or delegated authentication models depending on your platforms. The point is the same: users can access shared applications and collaboration tools without resetting passwords, changing usernames, or switching sign‑in portals on day one.
Why it accelerates: fewer user disruptions, fewer helpdesk tickets, fewer cutover dependencies, faster onboarding of acquired employees into shared tools.
How it stays safe: enforce baseline authentication strength, limit access scope, and apply consistent policy at the resource boundary (where shared applications live).
Lever B: Standardise security policy before standardising platforms
A merger often combines two “reasonable” security postures that are not identical. If you immediately unify platforms, you inherit every mismatch at the worst possible time. If instead you unify policy enforcement at the access boundary, you can get consistent outcomes (like MFA requirements and conditional access rules) even while systems remain separate.
Why it accelerates: you reduce debate and rework by agreeing on baseline controls early, and you avoid waiting for full platform consolidation to enforce them.
How it stays safe: policy enforcement becomes the common language; exceptions become visible and time‑bound rather than informal.
Lever C: Automate lifecycle controls early to prevent access sprawl
During mergers, organisational changes are frequent: internal transfers, new project teams, system decommissions, role changes, and sometimes reductions. If offboarding and entitlement cleanup are manual or delayed, risk increases daily.
Why it accelerates: automation reduces operational load and makes it feasible to scale integration beyond small pilot groups.
How it stays safe: deprovisioning is the single most effective control against lingering access; automation makes it consistent.
Lever D: Migrate data and collaboration workloads only after identity mapping is stable
When you move mailboxes, files, or collaboration artifacts across boundaries, identity mapping becomes the critical dependency. If mapping is not stable, the migration introduces broken sharing links, ownership confusion, and duplicated identities. Stabilising mapping early allows later migration waves to be predictable.
Why it accelerates: migrations become repeatable “factories” instead of bespoke rescue operations.
How it stays safe: controlled waves and pre‑validated mappings reduce the blast radius of mistakes.
5) Mandatory vs strategically deferrable integration elements
This section is the heart of your requirement. “Mandatory” means you should treat it as a gating condition for scaling integration. “Deferrable” means you can postpone it without compromising security or continuity—provided you have the mandatory controls in place.
5.1 Mandatory elements (non‑negotiable for safe acceleration)
Mandatory 1: Clear scope, governance authority, and decision rights
You need a single integration authority that can decide: what the Day‑1 model is, what is in scope, what the target operating model is, and how exceptions are handled. Without this, teams build parallel “bridges” that conflict.
Minimum viable deliverables:
- Day‑1 identity operating model (where authentication happens; where authorisation is evaluated; how access is requested and granted).
- A standard exception process with approvals and expiry dates.
- A single, agreed baseline security posture for shared resources.
Mandatory 2: Identity and application discovery (inventory and dependency mapping)
Acceleration without inventory is gambling. You must map: identity sources, directories, identity providers, key applications, authentication methods, and privileged accounts. This is the difference between planned change and surprise outages.
Minimum inventory categories:
- Authoritative identity sources (HR systems, directories).
- IdPs and authentication methods in use.
- Critical applications and their sign‑in patterns.
- Privileged accounts, admin roles, service accounts, and automation identities.
- External users, partner access, and collaboration relationships.
Mandatory 3: Strong authentication baseline and consistent policy enforcement for shared access
Before you scale cross‑company access, you must enforce strong authentication for shared applications and administrative actions. If one organisation has weaker controls, the combined environment inherits that weakness unless the boundary is protected.
Baseline expectations (typical):
- MFA for workforce access to shared corporate resources.
- Higher‑assurance controls for privileged accounts and sensitive systems.
- Consistent session controls and risk‑based conditional access where feasible.
Mandatory 4: Cross‑boundary access gating (explicit inbound/outbound rules and scopes)
Coexistence requires governance at the boundary: who can access what, from where, under what conditions. Without explicit inbound/outbound gating, “temporary collaboration” becomes broad, persistent access.
Minimum requirements:
- Scope access by user groups and by applications (not “everyone to everything”).
- Decide whether to trust external MFA and device claims; document the decision and its implications.
- Ensure emergency break‑glass paths are controlled and audited.
Mandatory 5: Automated joiner–mover–leaver controls and deprovisioning
Rapid onboarding is meaningless if offboarding is slow. Automated lifecycle control ensures that when someone changes role or leaves, access is removed quickly and consistently across the integrated footprint.
Minimum requirements:
- Automated disable/remove for departing users (or equivalent access removal) in both environments.
- Reliable revocation of access to shared apps and privileged roles.
- Periodic cleanup of stale accounts and entitlements.
Mandatory 6: Privileged access containment and admin boundary design
Merger periods often trigger “shared admin accounts” and ad‑hoc privilege grants. That creates severe risk. You must define admin boundaries, separate duties, and keep privileged actions auditable.
Minimum requirements:
- Limit who can administer identity systems and high‑impact resources.
- Ensure privileged elevation is controlled, time‑bound, and logged.
- Maintain emergency access accounts with strict governance.
Mandatory 7: Visibility, auditing, and incident readiness across both identity stacks
If you cannot see sign‑ins, admin actions, and policy decisions end‑to‑end, you cannot confidently scale integration. Visibility enables you to detect misconfigurations, abnormal sign‑in patterns, and privilege abuse early.
Minimum requirements:
- Centralised log collection for authentication and admin events.
- Alerting for suspicious sign‑ins and privilege changes.
- Incident runbooks that span both environments.
Mandatory 8: Compliance and privacy guardrails for cross‑organisation identity flows
Cross‑organisation identity sharing introduces privacy and regulatory implications, especially around attribute sharing, consent requirements, and data minimisation. You must validate the legal/compliance posture before scaling synchronisation or federation.
Minimum requirements:
- Document what attributes are shared and why.
- Apply data minimisation: share only what you must for access decisions and provisioning.
- Ensure your policies cover cross‑org collaboration and external identities.
5.2 Strategically deferrable elements (postpone safely, if mandatory controls are in place)
Deferrable A: Full consolidation into a single directory/tenant/forest/domain
A merged business can operate safely for a time with multiple identity environments if interoperability is controlled and policies are consistent at access points. Full consolidation is valuable—but it is not always required for Day‑1 productivity, and rushing it often increases outage risk.
Deferrable B: Perfect attribute harmonisation and “golden profile” unification
Early on, you typically need a subset of attributes to support authentication, authorisation, and provisioning to critical apps. Full harmonisation (job codes, department mappings, manager hierarchies, naming conventions) can be phased later.
Deferrable C: Long‑tail application refactoring and SSO modernisation
Focus first on the “must‑run” applications and collaboration tools. Lower‑impact apps can remain in existing auth patterns temporarily if the boundary is protected and risks are understood. Attempting to refactor everything at once slows the programme and increases outages.
Deferrable D: Advanced identity governance maturity beyond minimum viable controls
You need basic ownership, lifecycle, and entitlement patterns early. But advanced governance (deep role mining, extensive access certifications, complex segregation‑of‑duty automation) can be introduced once the identity model stabilises.
Deferrable E: Endpoint management consolidation and full device posture unification
Device trust is important, but endpoint stack convergence can be complex. If you can apply strong access controls and require appropriate device signals for sensitive access, full endpoint tool consolidation can be scheduled later.
Deferrable F: Complete eradication of legacy protocols and bespoke authentication
Legacy dependencies are common and often business‑critical. You can contain them with segmentation, restricted access pathways, and strong monitoring while you design long‑term modernisation. Eliminating everything immediately often causes business disruption.
6) A phased roadmap that accelerates and contains risk
Phase 0: Due diligence and rapid discovery (build the “map of reality”)
The goal is not perfect documentation; it is a sufficiently accurate inventory to avoid surprises. Identify identity stores, IdPs, authentication methods, privileged accounts, and critical applications. Classify apps by criticality and complexity.
Key outputs:
- Identity architecture map: sources of truth, directories, IdPs, trust relationships.
- Critical app catalogue: authentication methods and owners.
- Privileged access map: admin roles, service accounts, automation identities.
- External identity footprint: guests, vendors, partners, collaboration patterns.
Acceleration benefit: discovery reduces rework and prevents outage‑driven delays.
Phase 1: Day‑1 secure collaboration (controlled coexistence)
Enable cross‑company collaboration using an interoperability model appropriate to your technology landscape. Provide fast access to shared collaboration tools and priority business applications without forcing a mass credential cutover.
Safety requirements:
- Enforce baseline MFA and conditional access rules for shared resources.
- Scope access by groups and applications; keep it least‑privilege.
- Establish lifecycle automation to remove access when roles change or people leave.
- Ensure logging and incident response coverage across both environments.
Acceleration benefit: productivity is unlocked early, while deeper consolidation is decoupled.
Phase 2: Stabilise governance, reduce exceptions, and standardise access patterns
After Day‑1, the real risk is “exception debt”: temporary access, duplicated groups, inconsistent policies, and unmanaged external users. Phase 2 cleans this up.
Key actions:
- Convert ad‑hoc access into standard groups/roles and defined request flows.
- Apply consistent policies to the most sensitive apps first.
- Reduce and time‑bound exceptions; track exception burn‑down.
- Confirm lifecycle closure is working: leavers lose access quickly everywhere.
Acceleration benefit: stability enables scale; scale enables faster consolidation waves.
Phase 3: Progressive consolidation in waves (users, apps, and data)
Once mapping and governance are stable, start migrating users and workloads in repeatable waves. Decide wave criteria: business unit, geography, application dependency clusters, or risk profile.
Wave design principles:
- Start with low‑complexity cohorts to prove the factory.
- Migrate applications by dependency clusters, not random lists.
- Keep a defined rollback strategy for each wave.
- Validate post‑cutover access with scripted tests and monitoring.
Acceleration benefit: consolidation becomes predictable, not heroic.
Phase 4: Decommission duplicate systems and simplify (capture long‑term value)
Finally, retire what you no longer need: redundant IdPs, old directories, duplicate provisioning connectors, and legacy trust bridges. This is where the merger stops paying “identity tax.”
Acceleration benefit: operational cost drops and security posture becomes easier to maintain.
7) How to accelerate without creating an insecure “bridge” between two companies
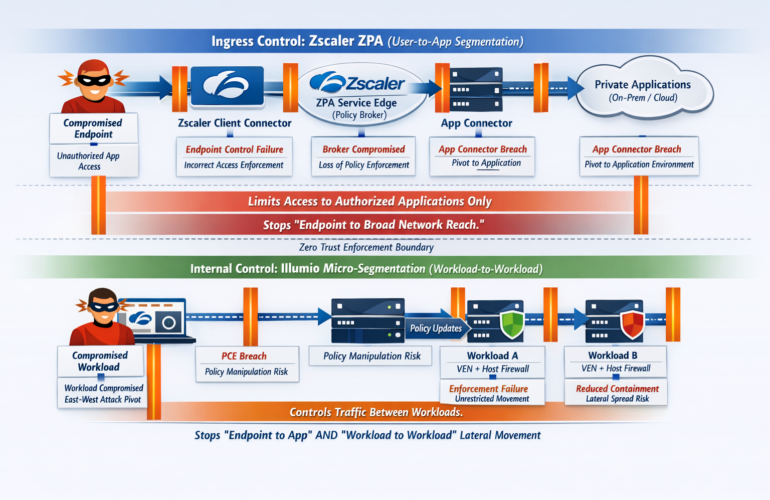
A merger creates a temptation: “Let’s just connect the networks and add a trust so everyone can work.” That approach is fast—but often insecure—because it expands lateral movement and makes compromise more damaging.
A safer approach is to create policy‑controlled pathways rather than open connectivity. Practically, this means:
- Prefer application‑level access enablement over network‑level trust.
Make users authenticate to an IdP with strong controls and then authorise access per application. Avoid broad “network implies trust” assumptions. - Limit scope by default.
Start with specific user populations and specific applications. Expand based on evidence and monitoring, not because “it seems fine.” - Treat admin access as its own programme.
Admin integration is different from end‑user integration. Keep it tightly governed and auditable. - Minimise shared attributes.
Share only the identity attributes required for access decisions and provisioning. This reduces privacy exposure and simplifies remediation if mappings are wrong. - Automate deprovisioning.
If you can create access quickly, you must remove it quickly. Manual offboarding cannot keep up with merger‑time change.
8) Common failure patterns (and what “safe acceleration” does instead)
Failure pattern 1: “Temporary exceptions” become permanent
In many mergers, exceptions become the true system of record. People bypass controls because it is faster, and then those bypasses persist. Safe acceleration makes exceptions explicit, approved, time‑bound, and measurable.
Better approach: maintain an exception register with owners and expiry, and track exception reduction as a programme metric.
Failure pattern 2: Identity sprawl and duplicate accounts undermine access control
Duplicate identities lead to orphaned access, confusion, and audit failure. This often happens when both companies create new accounts for each other without strong mapping.
Better approach: implement strong identity mapping early and restrict duplicate account creation. If coexistence requires external representations, manage them systematically and ensure lifecycle closure.
Failure pattern 3: Privilege sprawl during organisational churn
New teams form quickly. Admin roles get granted “temporarily.” Service accounts proliferate. This is where major breaches happen.
Better approach: treat privileged access as a first‑class workstream with time‑bound elevation, logging, and strict boundaries.
Failure pattern 4: Big‑bang migrations create widespread outages
Trying to migrate everything at once often breaks SSO, group memberships, file sharing, and workflow automation simultaneously.
Better approach: wave-based migration with rollback plans, pre‑tests, and post‑cutover monitoring.
Failure pattern 5: Lack of visibility turns small issues into major incidents
Without centralised sign‑in logging and alerting, you cannot distinguish “normal merger friction” from active compromise.
Better approach: make visibility mandatory and integrate incident response procedures across both identity environments.
9) Practical metrics: how to prove you are accelerating safely
You need metrics that measure both speed and control. Otherwise, the programme will optimise for visible progress while risk silently increases.
Speed metrics
- Time to enable Day‑1 collaboration for defined priority groups.
- Percentage of critical applications accessible under the baseline security policy.
- Migration wave throughput (for example, users or apps per wave).
- Helpdesk impact (sign‑in failures, password resets, access requests) before and after changes.
Safety metrics
- MFA coverage for workforce and privileged accounts.
- Privileged role assignment counts and the percentage of time‑bound elevations.
- Deprovisioning latency (time from leaving/role change to access removal across systems).
- Exception volume and average exception age (should trend down).
- Rate of anomalous sign‑in detections and time to investigation.
These metrics keep the programme honest: if speed is improving but exception debt and privileged sprawl are rising, you are accelerating in the wrong direction.
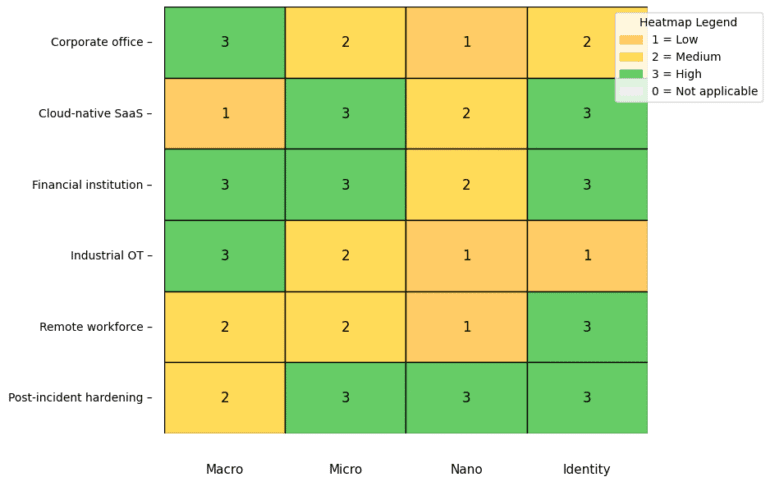
10) Recommended operating patterns for different merger scenarios (technology-agnostic guidance)
Although tooling varies, the operating patterns below work across most enterprise identity stacks:
Scenario A: Both companies have mature cloud identity platforms
Use controlled cross‑organisation collaboration and synchronisation patterns for Day‑1, unify baseline policy enforcement at the application boundary, then consolidate tenants and apps in waves once mapping stabilises.
Scenario B: One company is mature, the other is less mature
Avoid importing the less mature posture into the combined environment. Enforce the acquiring company’s baseline for shared resources from day one. Use interoperability so users can access required tools while you uplift security controls and inventory.
Scenario C: Significant on‑premises directory dependence
Be cautious with broad trust relationships. Prefer application‑level access enablement and segment legacy dependencies. Stabilise admin boundaries and logging early. Plan consolidation carefully once dependencies are known.
Scenario D: Multi‑org strategy (holding company, autonomy preserved)
Not every merger requires a single unified identity platform. If autonomy is desired, invest heavily in boundary policy, lifecycle automation, and consistent controls rather than forcing consolidation. The key is to avoid uncontrolled drift: autonomy without governance becomes fragmentation.
Conclusion: a disciplined “mandatory now, defer wisely” plan is the fastest route to value
The most reliable way to accelerate identity integration safely is to separate urgent collaboration needs from long‑term consolidation goals. Deliver Day‑1 productivity with controlled coexistence: strong authentication, explicit access gating, lifecycle automation, privileged access containment, visibility, and compliance guardrails. Then consolidate gradually in repeatable waves with stable identity mapping and standardised access patterns. This approach is faster in practice because it avoids outage-driven rework, reduces helpdesk load, limits blast radius, and prevents exception debt from becoming permanent architecture.
Summary of what is mandatory vs what can be deferred
Mandatory (before scaling access): governance authority and scope, inventory and dependency mapping, strong authentication baseline, explicit inbound/outbound access gating, automated lifecycle controls, privileged access containment, visibility and incident readiness, and compliance guardrails.
Deferrable (after stability): full tenant/forest/domain consolidation, perfect attribute harmonisation, long‑tail app refactoring, advanced identity governance maturity, endpoint tooling consolidation, and total legacy protocol eradication.