Microsegmentation locks down lateral movement by enforcing fine-grained policies between workloads. Two primary implementation models exist: agent-based, which installs software on each host, and agentless, which leverages network-level controls or third-party APIs. Both approaches have merits and trade-offs, and the right choice hinges on your environment, scale, and security objectives. This post intends to compare agent and agentless microsegmentation approaxches.
Understanding the Approaches
Agent-Based Microsegmentation
Agent-based solutions deploy lightweight software on every workload. These agents hook into the operating system’s networking stack—often via mechanisms like Windows Filtering Platform or kernel-level APIs—to monitor process-to-process interactions and enforce policies in real time. This tight integration offers deep visibility and direct control at the host level.
Agentless Microsegmentation
Agentless approaches rely on existing network infrastructure or cloud APIs to collect traffic metadata (via span ports, NetFlow, or service-provider APIs) and then push enforcement rules to network devices or virtual switches. No host-install footprint is required, but enforcement happens at chokepoints or distributed network controls rather than directly at the workload.
Agent and Agentless microsegmentation – Advantages and Disadvantages
Advantages of Agent-Based
- Fine-grained, process-level visibility and control for truly zero-trust policies
- Real-time enforcement embedded on the host, avoiding rerouting traffic through centralized chokepoints
- Bundled endpoint capabilities (file-integrity monitoring, EDR, deception) for extended threat detection
- Accurate segmentation policy generation based on observed inter-process communication
Disadvantages of Agent-Based Microsegmentation
- Requires deploying and maintaining agents on every host, adding operational overhead
- Potential performance impact due to in-host processing and telemetry collection
- Compatibility challenges with heterogeneous OS versions and container environments
- Increased patch and version-management complexity for large fleets
Advantages of Agentless Microsegmentation
- Rapid, footprint-free deployment that leverages existing switches, routers, or cloud APIs
- Minimal impact on host performance since all enforcement is off-host
- Simplified scaling in dynamic cloud or virtualized environments where adding agents is cumbersome
- Lower operational burden when workloads are ephemeral or frequently rebased
Disadvantages of Agentless Microsegmentation
- Limited to network-layer telemetry; lacks visibility into which processes generate traffic
- Reliance on hairpinning or centralized enforcement points can create bottlenecks and single points of failure
- Inability to directly enforce policies on intra-host “east-west” traffic without native host integration
- Gaps when cloud APIs don’t expose sufficient flow detail, leading to blind spots in dynamic environments
Product Considerations
Below is a high-level look at how leading solutions map to these models:
| Approach | Typical Vendors | Enforcement Method |
|---|---|---|
| Agent-Based | Illumio; Cisco Secure Workload; CrowdStrike Falcon | Host-resident agents using OS APIs |
| Agentless | VMware NSX-T; AWS Security Groups; Azure NSG | Network devices; cloud-provider APIs |
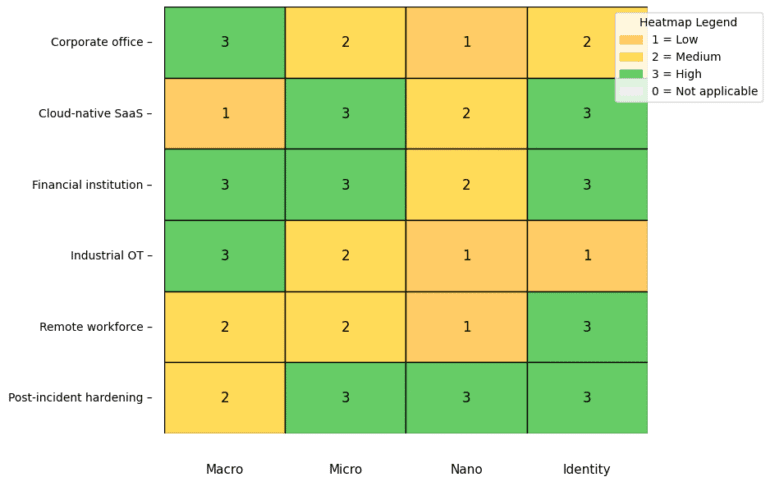
Choosing the Right Model
- Environment Complexity
- If you run mixed OS/container workloads and need deep process context, agent-based is ideal.
- If you operate purely cloud-native environments and prioritize no-touch deployment, agentless wins.
- Performance and Scale
- For ultra-low latency or high-throughput systems, minimize host overhead with agentless.
- In smaller, high-security clusters, the visibility of agents outweighs their resource footprint.
- Operational Overhead
- Agentless simplifies patch cycles and upgrades since there’s no host-side software.
- Agent-based requires robust software-management pipelines but delivers richer telemetry.
- Compliance and Audit
- Regulatory regimes demanding proof of per-process isolation often favor agent-based solutions.
- Network-only controls may suffice for less stringent environments or internal segmentation needs.
Conclusion
Agent-based and agentless microsegmentation each fill different niches. Agent-based provides unparalleled visibility and control at the cost of operational complexity, while agentless offers rapid, scalable deployment with coarser granularity. Align your choice with your security posture, performance requirements, and team capabilities.
For the next steps, consider:
- Mapping your current network/tactical controls to identify blind spots
- Running a proof-of-concept to measure performance impacts and visibility gains
- Integrating microsegmentation data with SIEM or XDR tools for unified monitoring
Beyond traditional microsegmentation, emerging trends include identity-driven segmentation—binding policies to user or service identities rather than IPs—and AI-powered policy recommendations that adapt in real time. You might also explore service mesh architectures (e.g., Istio, Linkerd) for layer-7 segmentation in containerized environments or unified zero-trust platforms that blend network, host, and identity contexts into one enforcement plane. Let me know if you’d like to dive into any of these future-focused topics!